Answers
Related Questions
Kevin is scanning old images from his college library. He might use these scanned images in the college magazine. He might also use them on the college website. What is the best practice for Kevin to follow when scanning the images?
A.
scan the images with 72 DPI
B.
scan only the images that are ideal for a website
C.
scan the images with 150 DPI
D.
scan the images with 600 DPI
E.
scan the images that are ideal for a magazine
Answers
Answer: D. Scan the images with 600 DPI
Explanation:
Answer: D. Scan the images with 600 DPI
Explanation: Correct for Plato/Edmentum
You were recently hired by a small start-up company. The company is in a small office and has several remote employees. You have been asked to find a business service that would accommodate the current size of the company, but would also be able to scale as the company grows. The service needs to provide adequate storage, as well as additional computing power. Which cloud service model should you use
Answers
Answer:
Infrastructure as a Service (IaaS)
Explanation:
Infrastructure as a Service, are services based online that provide a client with required server infrastructures including networking services, storage services, virtual environment services, security, processing services based, and scaling by using high-level API's that redirects the low-level data of the underlying network on a leasing or rent arrangement, such that the operation and maintenance cost of the servers are taken care of by the service provider.
Examples of hardware that computes on a network can share are the operating system and the web browsers
Answers
Answer:
False.
Explanation:
The hardware component of a computer can be defined as the physical parts or peripherals that enables it to work properly. Some examples of hardware components are monitor, speaker, central processing unit, motherboard, hard-drive, joystick, mouse, keyboard, etc.
A software component of a computer comprises of software application or program that are used by the computer to manage or control software application, computer hardware and user processes. Some examples of software components are operating system, registry keys, antivirus, media player, word processor, etc.
In conclusion, the hardware components of a computer are the physical parts that can be seen and touched while the software components cannot be touched but rather are installed as a program.
Hence, examples of software but not hardware that computers on a network can share are the operating system and the web browsers
Which of these is a discipline?
software manager
customer service specialist
help desk technician
software engineering
Answers
Answer:
Option D
Explanation:
Discipline here refers to any educational course in which a person studies.
software manager , customer service specialist and help desk technician are basically the job designations and not discipline in which one can pursue study.
However, software engineering is a discipline as one can educate himself/herself in this discipline and become a software engineer.
Hence, option D is correct
what is computer assisted translation
Answers
Answer:
the use of software to assist a human translator in the translation process.
Explanation:
Which line of code converts 3 to 3.0?
int(3)
type(3)
float(3)
single(3)
Answers
Answer:
float
Explanation:
The cell is intersection of column and row. true or false
Answers
Answer:
True
Explanation:
where a row and column meet. Columns are identified by letters (A, B, C), while rows are identified by numbers (1, 2, 3). Each cell has its own name—or cell address—based on its column and row
~Hope this helps
Answer:
True
Explanation:
How is the OR (||) logical operator used?
PLS HURRY
Answers
Answer:
The answer is below
Explanation:
A logical operator is a symbol or word used to connect two or more expressions such that the value of the compound expression produced depends only on that of the original expressions and on the meaning of the operator. Common logical operators include AND, OR, and NOT.
Lorann sends messages to Aiden that always go into Aiden’s Junk E-mail folder. Which process would best correct this problem so that Lorann’s messages no longer go into Aiden’s Junk E-mail folder?
A. adding Aiden to the Safe Senders list
B. adding Aiden to the Safe Recipients list
C. adding Lorann to the Safe Senders list
D. adding Lorann to the Safe Recipients list
Answers
Answer:
b
Explanation:
click on the _____button to move the selected text in the centre of the page (justify /centre)
Answers
Answer:
centre
Explanation:
In VPython, which line of code creates a ball five units away from the user from the center?
ballPosition = _______
myBall = sphere(pos = ballPosition)
vector(0, 0, -5)
vector(0, -5, 0)
vector(-5, 0, 0)
Answers
The line of code creates a ball five units away from the user from the cente is ballPosition = vector(0, 0, -5)
What is python code?In Python, there is found to be a generally used coding language such as HTML, etc.
Know that it is often used in programming and software creation and as such, having the ballPosition = to be vector(0, 0, -5) myBall = sphere(pos = ballPosition) is the right thing to do.
Learn more about VPython from
https://brainly.com/question/26497128
#SPJ2
Imagine you are the human resource director for a small video game company that employs around 20 coders, managers, artists, etc. You're in charge of writing the safety rules and regulations for the company. Provide at least four discrete rules you would implement
Answers
Answer: maybe not put cheats no secret or easter eggs or hard challenges im not sure
Explanation:
The four discrete rules one would implement can be
Provide no confidential company information to anyone who is not an employee of the company.Acknowledge sources obtained from other people's games or anything else with a copyright claim.Avoid abusing your power by cheating or abusing the games to benefit yourself or your associates.Maintain a positive workplace culture and show the utmost respect to everyone to increase productivity.What is a manager?A manager refers to a person who is responsible head of any project and helps in arranging the resources, checking the progress, and timely completion of it in order to achieve the vision and goal of the organization.
Preventing workplace diseases and injuries, as well as the suffering and financial burden they can bring on employees, their families, and employers are the fundamental objective of safety and health initiatives.
Learn more about managers, here:
brainly.com/question/29023210
#SPJ5
How do we know if we can believe the things on the internet?
Answers
Answer:
you have to check for reliability
Explanation:
Answer:
you can't always believe the internet some stuff is false are bended
Explanation:
yea
She goes to look at her
HTML code to see what is wrong line by line until she can figure out what she
messed up. Which process is Ana using?
A. Fragmentation
B. Identification
C. Pinpoint
D. Debugging
Answers
The process is Ana using is Debugging. Check below to see what the term is all about.
What is debugging used for?Debugging is known to be the act of working on how a given program runs, and also how it creates data so as to be able to defects and know issues in a given code.
Note that since she goes to look at her HTML code to see what is wrong line by line until she can figure out what she messed up, she is engaged in debugging.
Learn more about Debugging from
https://brainly.com/question/163290
#SPJ2
Which list shows a correct order of mathematical operations that would be used by a spreadsheet formula?
Answers
Answer:
It stands for Parentheses, Exponents, Multiplication/Division, Addition/Subtraction.
Which of the following images illustrates safe driving?
Answers
Answer:
bottom left
Explanation:
Answer:
keep your eyes on the road!!!!
You are working on a ticketing system. A ticket costs $10. The office is running a discount campaign: each group of 5 people is getting a discount, which is determined by the age of the youngest person in the group. You need to create a program that takes the ages of all 5 people as input and outputs the total price of the tickets. Sample input: 55 28 15 38 63 sample output: 42.5 the youngest age is 15, so the group gets a 15% discount from the total price, which is $50 - 15% = $42.5
Answers
Answer:
Explanation:
The following program is written in Java. It takes 5 inputs of int values for the ages of each member in the group. Then it loops through all of the ages and chooses the youngest age. Finally, it applies that age as a discount to the final price which would be $50, outputting the final discounted price. The output for the test case provided can be seen in the attached picture below in red.
import java.util.Scanner;
class Brainly
{
public static void main(String[] args) {
Scanner in = new Scanner(System.in);
int[] person = new int[5];
System.out.println("Enter age of individual 1: ");
person[0] = in.nextInt();
System.out.println("Enter age of individual 2: ");
person[1] = in.nextInt();
System.out.println("Enter age of individual 3: ");
person[2] = in.nextInt();
System.out.println("Enter age of individual 4: ");
person[3] = in.nextInt();
System.out.println("Enter age of individual 5: ");
person[4] = in.nextInt();
int youngest = person[0];
for (int x = 0; x < person.length; x++) {
if (person[x] < youngest) {
youngest = person[x];
}
}
double discount = 1 - (((double)youngest) / 100);
double output = 50 * discount;
System.out.println("Total Price: " + output + " the youngest is " + youngest);
}
}
Which of the following are causes of a run-time error. Choose all that apply.
A user enters a numeric value when a text value was expected.
A user enters text and numeric values.
A user enters a text value when a numeric value was expected.
A user enters a negative number when a positive number was expected.
Answers
Answer:
A C D
Explanation:
just did it
Answer:
A. A user enters a numeric value when a text value was expected.
C. A user enters a text value when a numeric value was expected.
D. A user enters a negative number when a positive number was expected.
Explanation:
Select the correct answer from each drop-down menu.
Complete the following sentences.
_________ effort is an important and necessary factor for the success of any project. In software development projects,
_______team members carry out several tasks to ensure the quality of the process and the final product.
Options for the first box are: managers, A teams, an individuals
Options for the second box are:internal, specific, external
Answers
Answer:
First, A teams, Second ,Specific
Explanation:
the _____tool is used to move the selected text to the right of the page ( align text right. / Align text left)
Answers
Answer:
align text right
Explanation:
subscribe to twomad or you are cringe for the rest of your life kid
Answers
Answer:
What if I don't want to?..........
What is fish processing?
Answers
which feature of project management includes monetary compensation for the employees
Answers
Answer:
Extrinsic compensation
Explanation:
The feature of project management that includes monetary compensation for employees is the Extrinsic compensation.
Extrinsic compensation is reward ( tangible ) given to workers/employees by the management of a project for the speedy completion of a task or for the completion of a specific task . It can in the form of monetary compensation or non-monetary compensation.
example of Non-monetary compensation includes certificate of honor, medical insurance .
example of monetary compensation includes : work Bonuses , salaries
I CANT DO SKIN MODS ON BRAWLHALLA RIGHT!!!! IM SO MADDDDDDDDDDD
Answers
I'm better then u in brawhlla
In today's e - commerce world, 'Disintermediation' may only affect intermediaries who are not performing value added services to customers. Do you agree with this statement? Explain why?
Answers
Answer:
No
Explanation:
Although 'Disintermediation' does affect these intermediaries I believe it also affects those that 'are' providing valuable services. This is because many other factors come into play when deciding to reduce intermediaries. Sometimes when a company has various intermediaries, a single one can provide the same value as two, therefore, for the company, it is more valuable to reduce the number of intermediaries that they have and provide more resources to fewer intermediaries so that they perform better for less pay. This is one of a few reasons why it can affect any intermediary, not just the ones that do not provide value.
Stages of reverse engineering
Answers
Answer:
Capture Data, Refine the Model, and then Manufacture it.
Explanation:
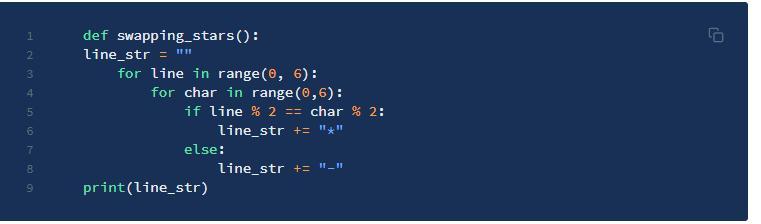
what's wrong with this python code i don't know what's wrong with both of them
Answers
Answer:
Keep it in the format
first one:
def swapping_stars():
line_str = ""
for line in range(6, 8):
for char in range(0, 6):
if line % 2 == char % 2:
line_str = line_str + "*"
else:
line_str = line_str + "-"
print(str(line_str))
swapping_stars()
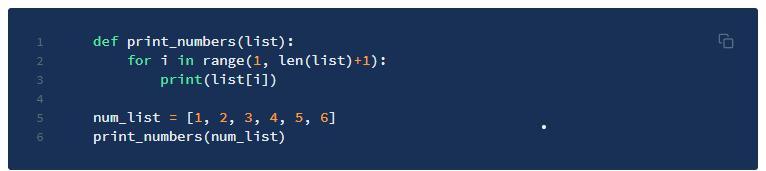
second one:
if you want it to go:
23456
def print_numbers(list):
for i in range(1, len(list)):
print(str(list[i]))
num_list = [1, 2, 3, 4, 5, 6]
print_numbers(num_list)
if you want it to go
123456
def print_numbers(list):
doneONE = False
for i in range(1, len(list)):
if not doneONE:
print(str(list[i] - 1))
doneONE = True
print(str(list[i]))
num_list = [1, 2, 3, 4, 5, 6]
print_numbers(num_list)
Explanation:
What requirements are necessary in order for you to share a file?
Check all that apply.
You own it.
You commented on it.
You can edit.
You know about the topic of the document.
Answers
Answer:
I. You own it.
II. You can edit.
Explanation:
A file can be defined as a computer resource that avails end users the ability to store or record data as a single unit on a computer storage device.
Generally, all files are identified by a name and type such as audio, image, video, document, system, text, etc. Each type of files can be transferred or send from one computer node to another computer node through the use of a wired or wireless connection and with the necessary level of permission.
The requirements which are necessary in order for you to share a file are;
I. You must own the file. This simply means that you have the authority to share the file and have it saved on your device.
II. You have the permission or required credentials to edit the file. A read-only permission cannot be used to edit a file but a full permission can be used.
What is the check digit for the following original product number: 140501941 ? *
a)10
b)7
c)5
d)2
Answers
Explanation:
I think it is 7, but I could be wrong..... sorry
A(n) ________ HTML tag is used to mark information about the page.
Metadata
Mead
img
Hyperlink
Answers
An Metadata HTML tag is used to mark information about the page.
What are HTML element?An HTML element are known to be a kind of HTML document parts, one of plenty types of HTML nodes.
Note that an HTML document is made up of a tree of some specific HTML nodes, example is text nodes, and HTML elements, that are said to add semantics and formatting to some areas of document. And so, Metadata HTML tag is used to mark information about the page.
Learn more about HTML tag from
https://brainly.com/question/9069928
Answer: metadata
Explanation: got it right on edgen